Archive for July 2011
Pattern Matching Hyphen-Minus Sign in Bash
I was trying to use the sed command to perform some changes to a text and stepped into an interesting “problem”; pattern matching the minus-hyphen (-) symbol.
Assume we have the following text:
something SoMeThiNg some-thing soMe_thing
and we want to match all the different versions of the word with one expression (one by one).
My initial idea was to use this regular expression:
's/[a-zA-Z\-\_]*/matched/' |
Naturally, I tried to escape the – sign. As you can see from the output, this doesn’t work:
$ sed 's/[a-zA-Z\-\_]*/matched/' test matched matched matched-thing matched |
The minus sign is not matched, because of its special meaning (setting ranges). In order to make the expression work, you need to move the “-” either in the beginning or in the end of the expression:
$ sed 's/[a-zA-Z\_-]*/matched/' test matched matched matched matched $ sed 's/[-a-zA-Z\_]*/matched/' test matched matched matched matched |
and leave it un-escaped!
Microsoft Translator Bot (TBot)
Have you ever heard of Microsoft’s Translator Bot, known as TBot? It is a bot that you can add as a contact in your Windows Live (msn) account and can be used for automated translation. You just need to add mtbot@hotmail.com as a friend. Read more here.
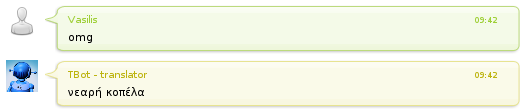
I post this because I was playing with TBot and I stepped into a very nice English to Greek Translation:
Everyone knows what “omg” stands for, right? Oh My God..
Well, “νεαρή κοπέλα” is “young girl” in Greek :-O.. Even TBot knows that:

Top 25 Most Dangerous Software Errors
The 2011 CWE/SANS Top 25 Most Dangerous Software Errors is a list of the most widespread and critical errors that can lead to serious vulnerabilities in software. They are often easy to find, and easy to exploit. They are dangerous because they will frequently allow attackers to completely take over the software, steal data, or prevent the software from working at all.
The Top 25 list is a tool for education and awareness to help programmers to prevent the kinds of vulnerabilities that plague the software industry, by identifying and avoiding all-too-common mistakes that occur before software is even shipped. Software customers can use the same list to help them to ask for more secure software. Researchers in software security can use the Top 25 to focus on a narrow but important subset of all known security weaknesses. Finally, software managers and CIOs can use the Top 25 list as a measuring stick of progress in their efforts to secure their software.
Find the list here.